Important to Know About Gozi 2 Infection
Gozi 2 Trojan can perform a lot of harmful activities on your PC after installing. It can try to delete some important host files, and create some other new files onto the system. So you may find a lot of unknown files, .exe, .dll process on your task manager. In addition, Gozi 2 infection also may block some certain programs. Like blocking firewall and antivirus programs, so you may get some error messages.
Gozi 2 infection changes computer settings secretly to allow it to hide in registry entries which would make it more difficult to be removed. After changing the settings of the system, you may get many issues like unwanted redirects to malware sites, getting a bunch of pop-up ads or links when open the default web browsers. Like other Trojan virus, it will build a bridge to outside threats, so your computer may be ready to get infected with more unknown infections. Moreover, Gozi 2 Trojan will open a backdoor for the remote hackers, stealing your valuable data and sensitive information and so on. So you have to remove Gozi 2 virus from your PC in a hurry up.
Associated Changes with Gozi 2 Infection
1. Unexpected redirect of Internet Browser, Firefox or Google Chrome.
2. Modified homepage and easily frozen or crashed web browser.
3. Out-of-nowhere ads popups on certain regular webpages.
4. Severely lagged response with high CPU consumption.
5. Automatically added shortcut on desktop linked with ads pages.
6. Disappearing links in bookmark folders and Favorites list.
7. Disabled Firewall and out-of-work Windows security center.
8. Unauthorized extensions, plug-ins, add-ons and so on.
9. Download, upload other dangerous processes or applications
Two Lessons to Get Rid of Gozi 2 Infection from Windows XP/ Vista/7/8
Lesson 1: Gozi 2 Infection Manual Removal
Before you performing manual steps, please back up all your Windows registry and important files. For any mistake may cause loss of precious data.
Step one: Reboot your computer into Safe Mode with Networking
Windows XP/ Vista/7:
Turn your computer off and then back on and immediately when you see anything on the screen, start tapping the F8 key on your keyboard.
Using the arrow keys on your keyboard, select Safe Mode with Networking and press Enter on your keyboard.

For win8:
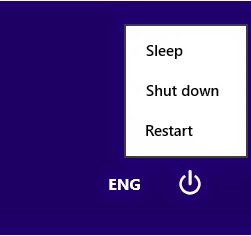
Reboot your computer in safe mode with networking.
Press the Power button at the Windows login screen or in the Settings charm. Then, press and hold the ” Shift” key on your keyboard and click Restart.
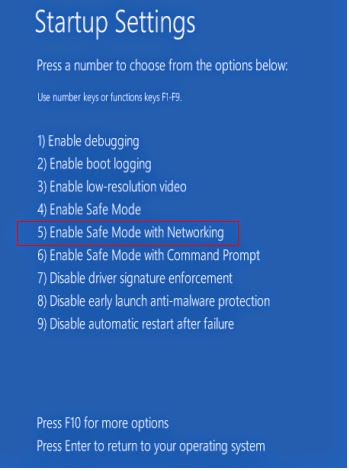
Click on Troubleshoot and choose Advanced Options. Then click on Startup Settings and select Restart. Your PC will restart and display nine startup settings. Now you can select Enable Safe Mode with Networking.
Step two: Show hidden files
a) Open Control Panel from Start menu and search for Folder Options;
b) Under View tab to tick Show hidden files and folders and non-tick Hide protected operating system files (Recommended) and then click OK;
c) Click on the “Start” menu and then click on the “Search programs and files” box, Search for and delete these files generated by this Trojan:

%AppData%\[RANDOM CHARACTERS]\[RANDOM CHARACTERS].exe
%AllUsersProfile%
%AllUsersProfile%\Programs\{random letters}\
%AllUsersProfile%\Application Data\~r
%AllUsersProfile%\Application Data\~dll
*For Windows 8 users
a. Open Windows Explorer from Start screen, navigate to View tab. At Show/Hide column, tick both file name extensions and Hidden items and hit Enter.

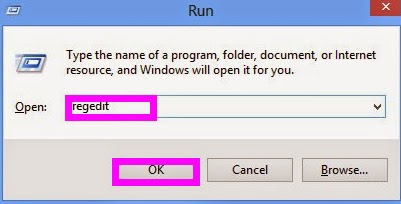
Step three. Examine following entries respectively. Seeing any suspicious key value started with Run, right click on it and select Delete.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\Current Version
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Shell Folders Startup=”C:\windows\start menu\programs\startup
Lesson 2: Gozi 2 Infection Automatic Removal with Removal Tool
For manual removal of this infection needs to know more about special computer skills, if you have no more knowledge, please don’t do any trial.
1: Download Removal Tool by clicking the below icon. (if you feel your computer sluggish, please restart your PC and then sign in safe mode with networking.)
2: Installation process:
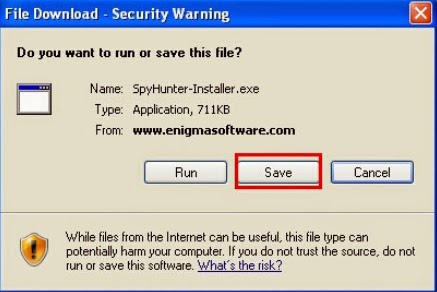
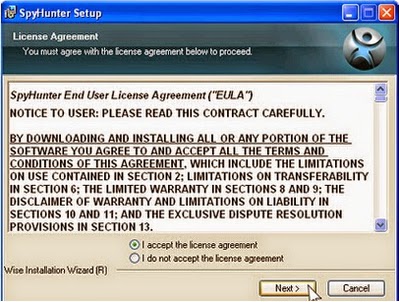
1) Check out the "File Download", and press "Save" to save SpyHunter file. “Save” the SpyHunter file on your Desktop.

2) Double click on the installation file and you will be prompted with a license agreement. Please read through the license agreement and check the box stating that you agree to the terms and click "Next."


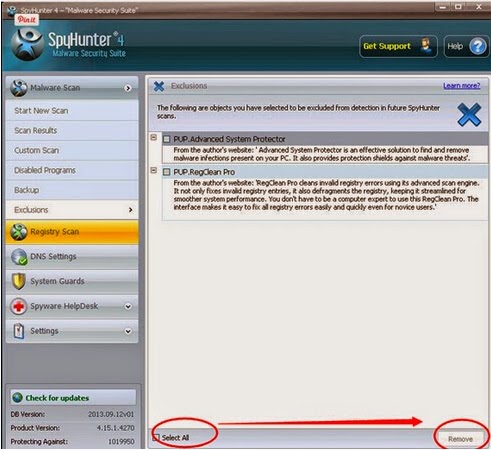
3: After the installation has been successfully completed, SpyHunter will start scanning your system automatically.

4: You should now click on the Remove button to remove all the listed malware.
Double Check with RegCure Pro
After the scanning with SpyHunter, to make sure your computer safe, please check it with RegCure Pro again.
RegCure Pro is a tool to fix the common problems that cause PCs to become slow, sluggish and erratic performers. This software is a fantastic cleaner. It gets rid of active malware and viruses, registry errors, junk files, unneeded process and programs that slow your PC down and make for long startup times.
1.Click here to download RegCure Pro

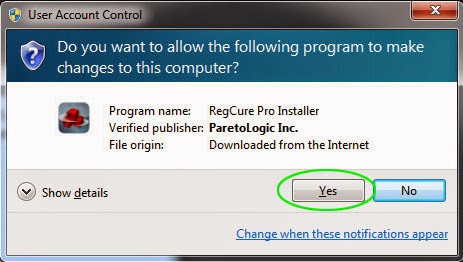
1) You will need to click Save or Run to install the application. (If you choose to save the application, we recommend that you save it to your desktop and initiate the free scan using the desktop icon.
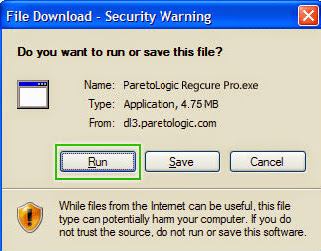
2) Once the file has downloaded, give permission for the Setup Wizard to launch by clicking the "Next" button. Continue following the Setup Wizard to complete the RegCure Pro installation process.
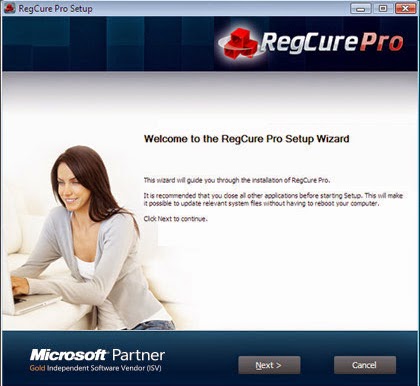
2. Click “Start Scan” to do a scan with your system.

3. Delete all detected issues and fix PC with RegCure Pro.

Notice: Gozi 2 Infection is very dangerous that attack system from all sides. If you want to protect your PC from getting infected with more virus or malware, keeping away from remote hackers, you have to remove this Trojan virus. Manual removal is a very complex process, if in case you have no idea with it, please remember that the best choice to uninstall this Gozi 2 Trojan is using top and useful removal tool.
No comments:
Post a Comment